Concept of the service
You cannot rest assured only with the deployment of an endpoint security product. Advanced detection and security operations are essential to protect corporate assets from increasingly sophisticated cyber attacks and create a more flexible and productive business environment.

Endpoint Security Product

Advanced Detection by Engineer

Security Management
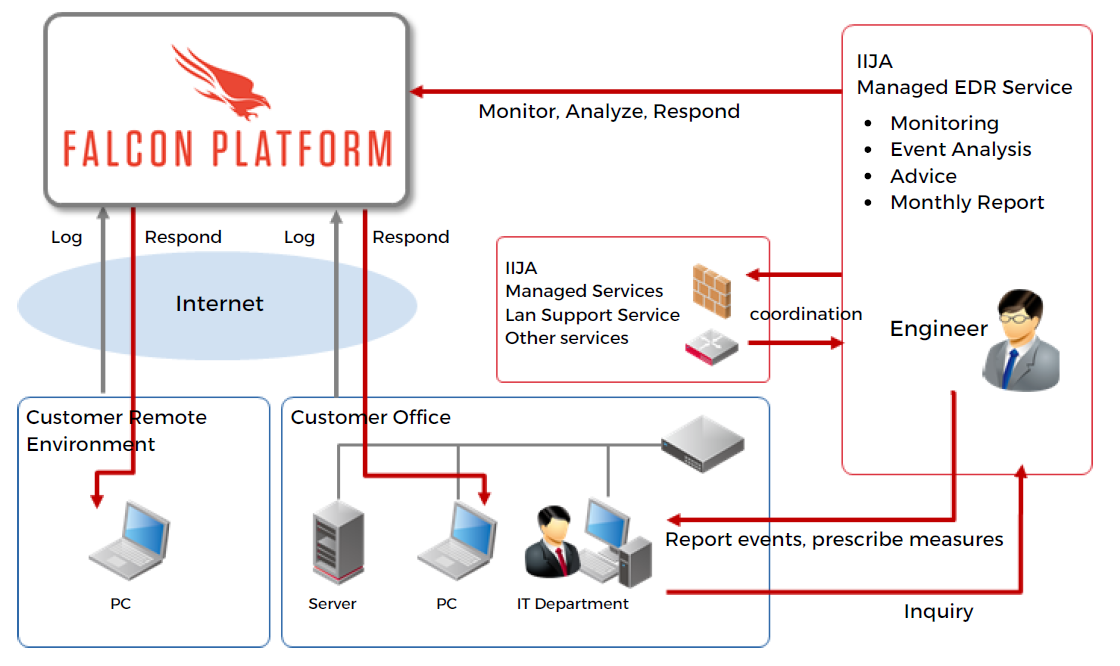
Service Features
IIJ America has partnered with an endpoint protection industry leader, CrowdStrike. Our security engineers will assist you with day-to-day security management.
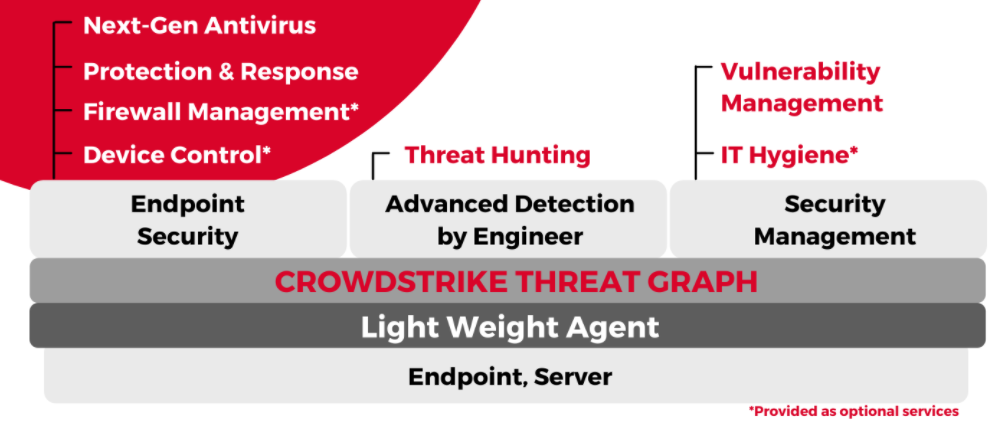
CROWDSTRIKE FALCON functions
Falcon platform provided by CrowdStrike overcomes the limitations of traditional security solutions, and has integrated key elements of endpoint security into one cloud-based solution.
-
Provided as optional services
Next-Gen Antivirus
Detect known and unknown threats with a combination of AI, behavioral detection,machine learning algorithms,and exploit mitigation.
Protection & Response
Monitor endpoints 24/7, visualize security events and enable thorough investigation of the incident and contain infected endpoints remotely.
Device Control*
Check the usage of USB devices on an endpoint, with the ability to disable target USB devices.
Threat Hunting
CrowdStrike’s Security Expert Team (Overwatch Team) will monitor and analyze the data collected to detect the latest attacks.
Vulnerability Management
List of vulnerabilities and patches/updates that need to be applied for easy and comprehensive management.
Firewall Management*
Make easy to create, manageand enforce policies with a simple, centralized approach.
Service Outline
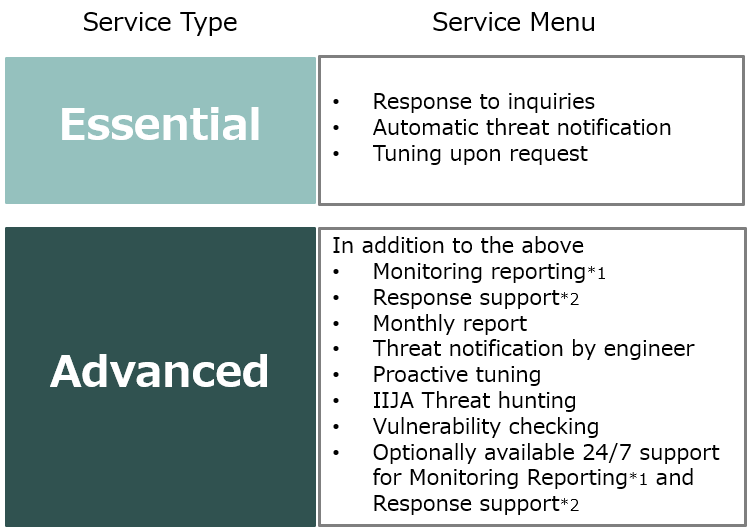
Service Types
Select a service type from differentservice levels.
Merits of Managed EDR Service
Once a Security Incident is detected, IIJ A’s Security Engineers will analyze the security logs to identify the origin of the incident, and will recommend how to prevent similar issues. (Advanced Type)
Pre-set responses will be put in to effect depending on the severity of the incident. Remote responses available for fastest response. (Standard/Advanced Type)
Customers who already have engaged with IIJA with IIJA managed Services and LAN Support service will be provided an comprehensive security advice for recommended actions and set-ups for their IT environment.